I will be presenting research results on how to detect malware on medical devices at USENIX HealthTech in Washington, D.C. on August 12th. Below is a summary of our research (lightly edited from the final paper). I would be happy to discuss the project at the workshop or before. We are particularly interested in collaborating with manufacturers and hospitals to further field test our prototype.
Health care networks are composed of general-purpose computers (e.g., desktop workstations) and embedded devices that perform specific functions and connect to the network for centralized control or configuration. A primary drawback of increasing connectivity is that all devices on the network---including embedded devices---are increasingly exposed to malware [1,2]. The U.S. Food and Drug Administration has recently acknowledged these risks by issuing a safety communication concerning cybersecurity.
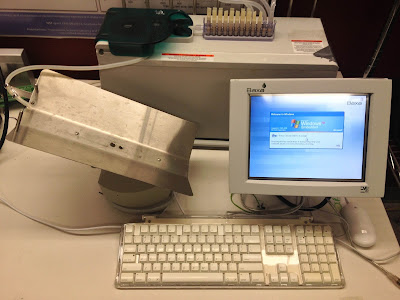 |
| This pharmaceutical compounder is a medical device running Windows XP Embedded. In a controlled lab, we repeatedly infected such devices with malware to evaluate the effectiveness of WattsUpDoc. |
Using WattsUpDoc, device owners can gain greater visibility into the behavior of the systems they own. WattsUpDoc can provide preliminary evidence of abnormal behavior, such as malware problems, signaling the need for further investigation. WattsUpDoc may also help to detect general abnormalities such as a failing hardware component or misconfigured software. With better visibility and earlier warnings, WattsUpDoc can help to detect problems that otherwise could lead to hazardous situations and harm.

No comments:
Post a Comment
All comments are moderated to prevent spam, so please pardon the delay while our anti-spam team looks at incoming messages.