We were sad to hear that Barnaby Jack, a skilled ethical hacker who applied his keen intellect and infectious enthusiasm to medical-device security, died in San Francisco on July 25. Among other accomplishments, he got a lot of technically inclined people interested in medical devices—which can only be good for the world. May he rest in peace. (Donations.)
When experts claim the sky is falling, we point out that you're just looking at the ground.
Tuesday, July 30, 2013
Friday, July 26, 2013
WattsUpDoc: Detecting malware on medical devices via an instrumented power outlet
I will be presenting research results on how to detect malware on medical devices at USENIX HealthTech in Washington, D.C. on August 12th. Below is a summary of our research (lightly edited from the final paper). I would be happy to discuss the project at the workshop or before. We are particularly interested in collaborating with manufacturers and hospitals to further field test our prototype.
Health care networks are composed of general-purpose computers (e.g., desktop workstations) and embedded devices that perform specific functions and connect to the network for centralized control or configuration. A primary drawback of increasing connectivity is that all devices on the network---including embedded devices---are increasingly exposed to malware [1,2]. The U.S. Food and Drug Administration has recently acknowledged these risks by issuing a safety communication concerning cybersecurity.
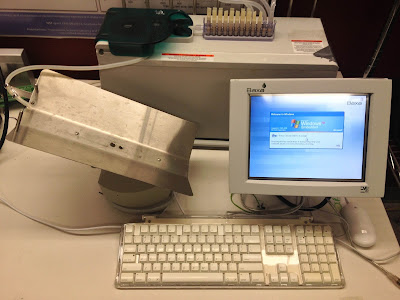 |
| This pharmaceutical compounder is a medical device running Windows XP Embedded. In a controlled lab, we repeatedly infected such devices with malware to evaluate the effectiveness of WattsUpDoc. |
Using WattsUpDoc, device owners can gain greater visibility into the behavior of the systems they own. WattsUpDoc can provide preliminary evidence of abnormal behavior, such as malware problems, signaling the need for further investigation. WattsUpDoc may also help to detect general abnormalities such as a failing hardware component or misconfigured software. With better visibility and earlier warnings, WattsUpDoc can help to detect problems that otherwise could lead to hazardous situations and harm.
Wednesday, July 17, 2013
USENIX HealthTech hosts medical device security panel from FDA, VA, and industry in DC
I am pleased to announce that representatives from FDA, the VA, and medical device manufacturing have agreed to participate in a technical panel on recent activity in the medical device security space. Early registration for the USENIX HealthTech Workshop ends on July 22. Note, this is a technical and research workshop. With a bit of policy to spice things up.
USENIX HealthTech Workshop on Safety, Security, Privacy, and Interoperability of Health Information Technologies
Monday, August 12, 2013
Hyatt Regency Washington on Capitol Hill
Washington, DC
The panel on "Health Data and Device Perspectives from Industry, Government, and Health Providers" takes place at 11AM and will focus on security and privacy related to recent news over the past year. Confirmed panelists include:

Brian Fitzgerald, Deputy Division Director, Division of Electrical and Software Engineering, U.S. Food & Drug Administration Center for Devices & Radiological Health
Ken Hoyme, Medical Device Consultant and Co-chair, AAMI Medical Device Security Working Group; Former Senior Fellow, Boston Scientific, Cardiac Rhythm Management
 Lynette Sherrill, Deputy Director, Office of Information Security, Field Security Office, Health Information Security Division, Department of Veterans Affairs
Lynette Sherrill, Deputy Director, Office of Information Security, Field Security Office, Health Information Security Division, Department of Veterans AffairsFor a refresher course, look back at the video recordings from the predecessor workshop, HealthSec.
-Kevin Fu
Thursday, July 11, 2013
Covered entities and medical device security
Mac McMillan has an interesting quote in a recent article, "FDA Warnings About ‘Cyberattacks’ Give CEs Leverage to Demand Better Security."
So where is OCR in all this? McMillan says the agency has been putting “pressure” on FDA and the Office of the National Coordinator for Health Information Technology (ONC) about this issue. However, OCR spokeswoman Rachel Seeger would say only that OCR had no “substantive” or “direct role in FDA’s guidance or warning.”
McMillan says there is talk of creating some kind of system for assessing medical device security features akin to HHS’s meaningful use certifications that apply to electronic health records. Only those that meet certain criteria, which include certain access controls, can be purchased with federal funds (RPP 9/12, p. 4). CMS and ONC maintain a list of certified EHRs.
A version of this question was discussed by panelists from CMS and FDA (audio recording conveniently below). In February 2012, I moderated a panel at the NIST Information Security & Privacy Board on the topic of economic incentives to improve medical device security. The audio recording and discussion questions can be downloaded from our blog post. The high bit: at the time, there were very few economic levers for covered entity to incentivize better cybersecurity in manufacturing of medical devices. The draft guidance from FDA may provide an important lever for covered entities so that patients ultimately have safer and more effective medical devices.
-Kevin Fu
-Kevin Fu
Public radio's Marketplace on medical device security
| Radio is hip. |
I presume the research that Dr. Castellanos refers to is this one from 2008. But there are plenty of other non-implantable devices that arguably bear more risk to public health by virtue of sheer quantity and area of attack surface. For instance, the incidents documented in our blog archive.
Subscribe to:
Posts (Atom)



